The ticket that never stops arriving
Most helpdesk teams know the feeling. Monday morning, the queue fills up. A third of the tickets (sometimes more) are some variation of the same request: "I can't log in," "My password expired," "I'm locked out."
This isn't an exaggeration. An HDI Research Corner survey of 339 IT support organizations found that, on average, about three out of every ten support tickets are related to password resets. In more than a third of support centers, password-related requests exceed 30% of total ticket volume. Separately, Gartner has estimated that 20-50% of all help desk calls involve passwords and resets. The range varies by organization, but the direction is consistent: it's a lot.
What makes this particularly frustrating for IT leads is that each one costs real money. Forrester Research estimates the cost of a single password reset at $70 when you factor in the fully-loaded cost of an IT staff member's time (ticket creation, the call or chat, verification, the actual reset, and documentation). One study of over 700 organizations found the average company spent enough on password resets to save $64,610 per year by switching to self-service. That's before counting the productivity loss for the employee who's locked out and waiting.
For IT managers trying to justify an AI IT help desk investment, password resets are the easiest ROI case to make: the volume is measurable, the cost is documented, and the resolution process is genuinely automatable.
This guide covers how AI actually handles password reset requests end to end: the conversation flow, the identity verification problem, the directory integration, and what the major ITSM platforms do differently.
How the manual process creates the problem
A typical manually-handled password reset goes something like this: a user realizes they're locked out, they submit a ticket or call the helpdesk, they wait in a queue, a technician picks it up, verifies the user's identity (sometimes rigorously, sometimes by asking their name), resets the password, documents the ticket, and closes it. Elapsed time: anywhere from 15 minutes to several hours depending on queue depth.
The problem isn't just the technician's time. It's the compounding. An organization with 500 employees might generate 15-20 password resets on a normal Monday. Each one is a context switch for a helpdesk tech who could be resolving something harder. Each one is a frustrated employee sitting idle. And because 89% of organizations require periodic password changes (most on a 90-day cycle), the volume is structurally guaranteed. It will never be zero.
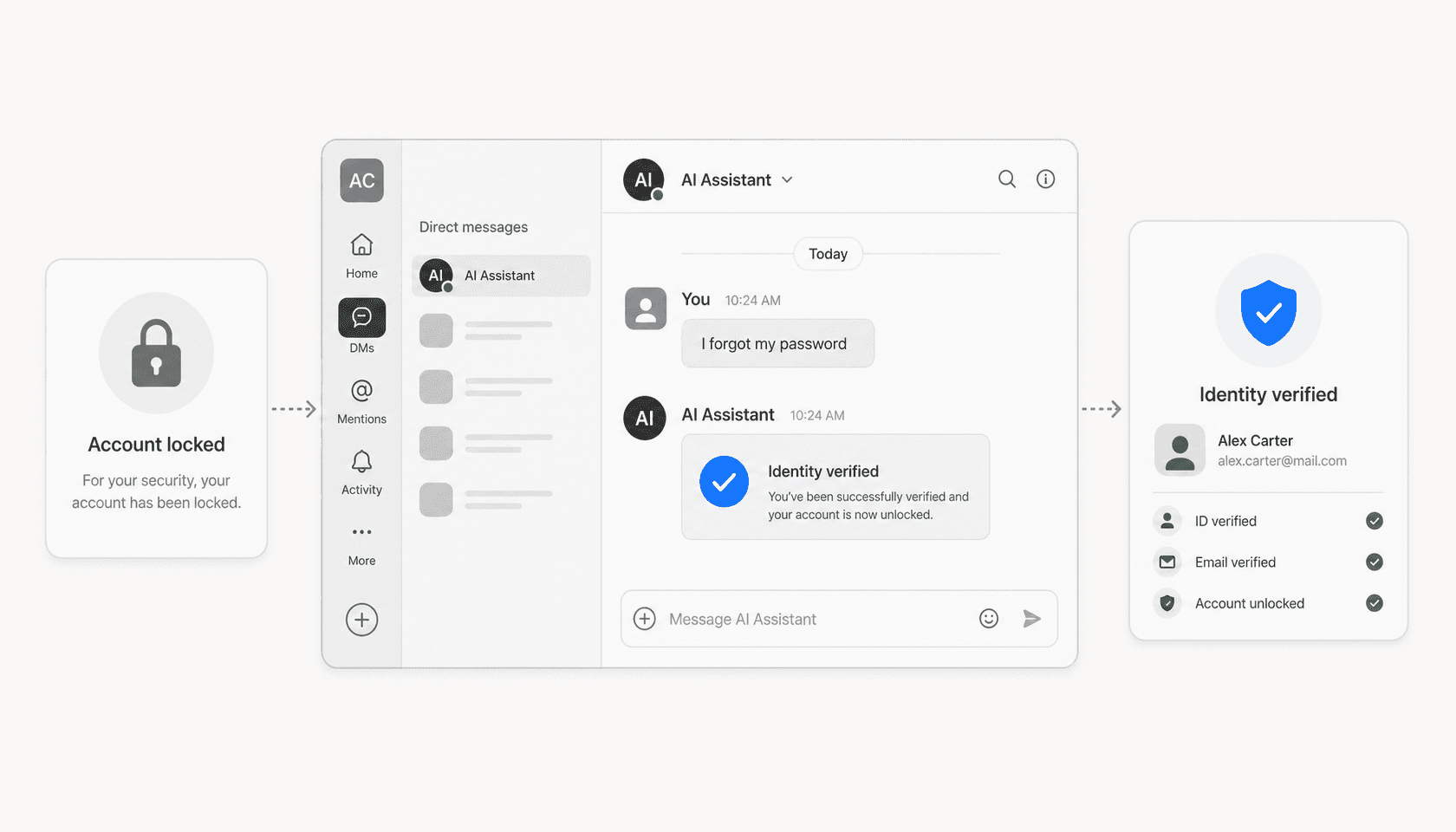
Self-service password reset (SSPR) has existed for years. The problem with older SSPR implementations is that they're clunky: separate portals that employees forget exist, security question flows that are easy to bypass, and no integration with the channels where employees actually work (Slack, Teams). AI changes the equation by bringing the reset flow into the conversation itself, with no portal to find and no separate interface to remember.
How AI handles a password reset request
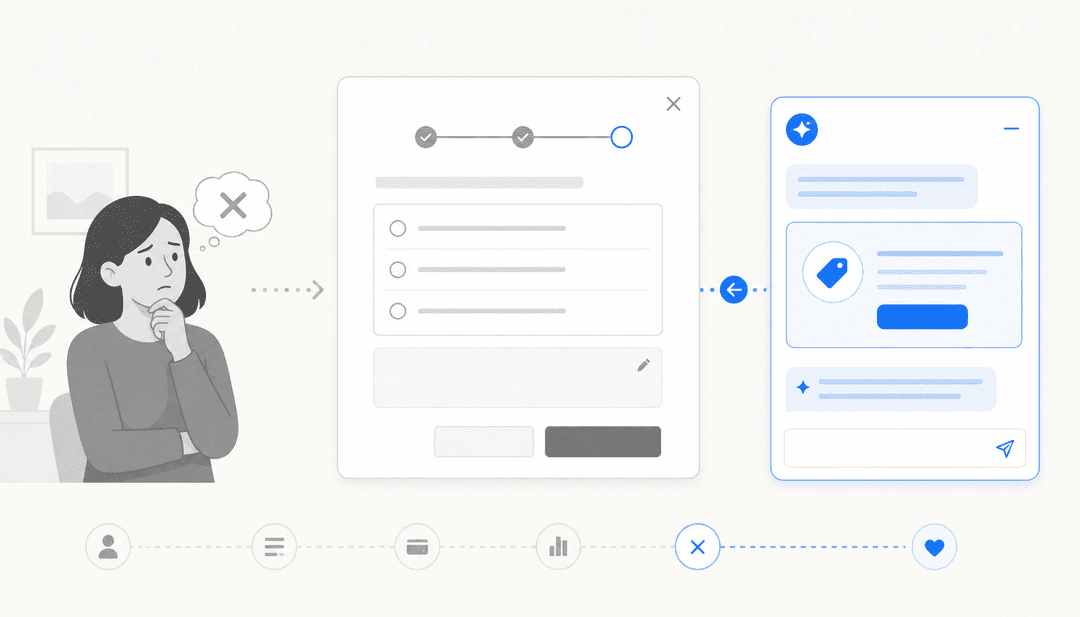
The process an AI-powered system follows is straightforward once you map it out:
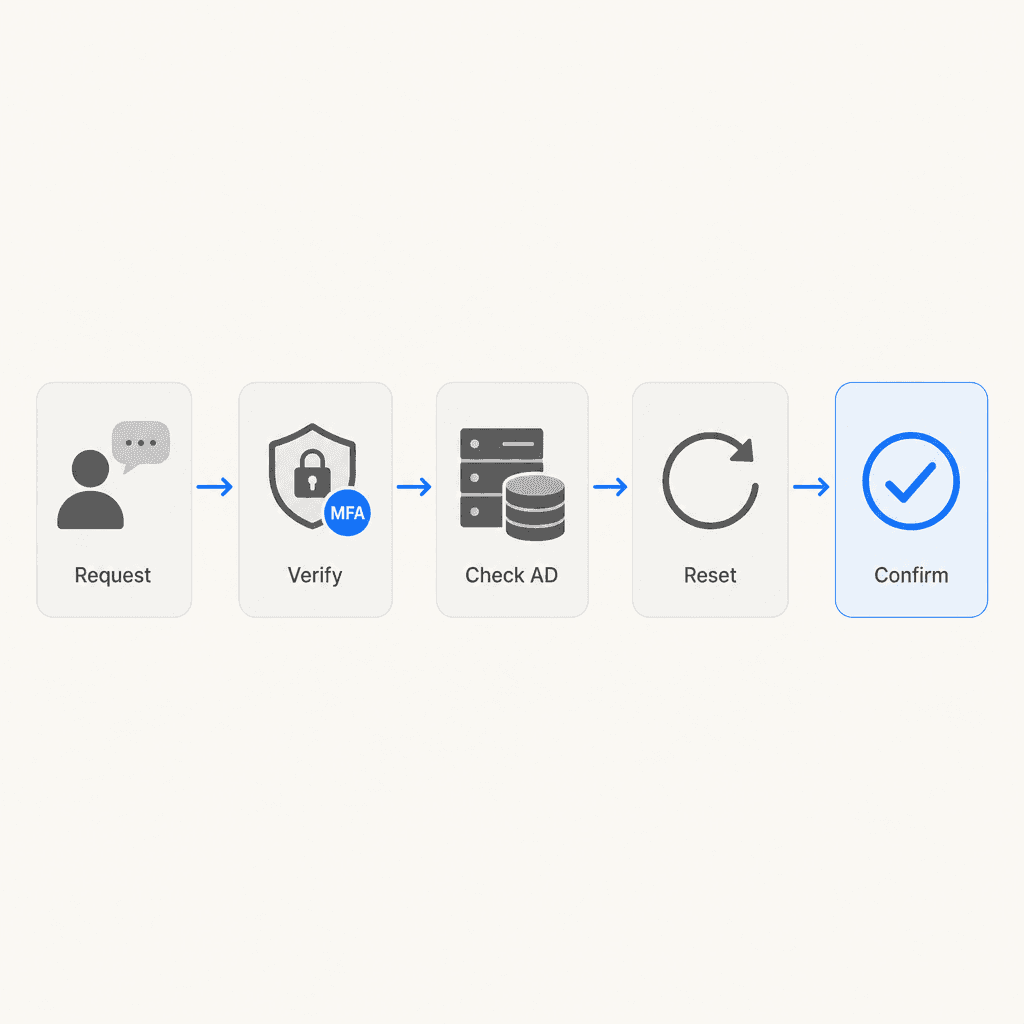
Step 1: Request detection. The employee sends a message ("I can't log in," "I forgot my password," "my account is locked") to a helpdesk bot in Slack, Teams, or a service portal. The AI recognizes the intent from natural language rather than requiring a specific keyword or form submission.
Step 2: Identity verification. Before touching anything, the system verifies the requester is who they say they are. This is the security-critical step. Modern implementations use one or more of:
- MFA challenge (push notification to the user's registered device or authenticator app)
- One-time passcode sent to a verified personal email or phone
- Manager approval workflow (the AI pings the user's manager, who approves within a time window)
- Hardware token verification
Security questions alone are considered weak: they're too easily social-engineered. Any serious deployment pairs at least one out-of-band verification with the request.
Step 3: Directory check. The AI confirms the account status in the connected identity provider (Active Directory, Azure AD/Microsoft Entra ID, Okta, or Google Workspace) and determines whether the account is locked, the password is expired, or login is blocked for another reason.
Step 4: Reset and unlock. With identity confirmed and the account status understood, the system issues the reset via the identity provider's API. The new temporary password (or a reset link) is delivered through a secure, verified channel.
Step 5: Confirmation and ticket closure. The system confirms the reset to the user, logs the ticket automatically, and marks it resolved. No human touches the ticket.
The whole sequence, when fully automated, takes under two minutes. The HDI data suggests manual resets average much longer when you account for queue wait time. That gap is where the ROI lives.
The identity verification challenge
The single biggest obstacle to fully automated password resets isn't the directory integration. It's verifying identity without a human in the loop.
The risk is real: social engineering attacks regularly target IT helpdesks because a successful impersonation results in account access. Attackers specifically target helpdesks with social engineering to gain unauthorized access and bypass MFA. If the AI is too easily convinced, it becomes a security hole.
The practical answer is to match your verification rigor to your account sensitivity. For standard employee accounts, an MFA push challenge to a pre-registered device is adequate. For privileged accounts (admins, finance, executives), require a higher bar: multiple verification factors, or route through a human reviewer. Most enterprise SSPR implementations let you set tiered verification policies by user group or role.
One thing to avoid: treating any single static factor (security questions, name + employee ID) as sufficient. The combination of something the user has (their phone) with something they can authenticate is the current floor for reasonable security.
Platform implementations
ServiceNow (with Moveworks)

ServiceNow bundles conversational AI password reset capability through its Moveworks integration, which became part of the platform following ServiceNow's $2.85 billion acquisition of Moveworks (completed December 2025). The ITSM plans now each include a "Moveworks for ITSM" SKU at the matching tier: Foundation, Advanced, and Prime.
Moveworks specifically cites password resets as one of the primary use cases for its conversational AI assistant. The platform connects to Active Directory, Azure AD, Okta, and other enterprise identity providers and can handle end-to-end resets through Slack or Teams without a technician. The newly launched "ServiceNow EmployeeWorks" product (the combined Moveworks conversational front door) is described as available "where employees already work and collaborate, whether in Teams, Slack, or on any browser."
ServiceNow does not publish dollar pricing. All tiers terminate in a "Get Custom Quote" CTA (source: ITSM Plans and Packages). The platform's own internal deployment of its Autonomous Workforce handles over 90% of employee IT requests autonomously — password resets being a primary category.
ServiceNow is the right choice for large enterprises with complex IT environments that want password reset automation embedded in a broader ITSM platform with incident, change, and asset management baked in. For smaller organizations, the implementation complexity and pricing model (custom quotes only) can be prohibitive.
Freshservice (Freddy AI)

Freshservice handles password resets through Freddy AI Agent — its 24/7 virtual agent that operates across Slack, Microsoft Teams, Microsoft 365 Copilot, and the service portal. The platform's documentation explicitly calls out password resets as a primary use case for no-code automated workflows: "Password reset functionality: One of the most common IT requests, password resets should be fully automated through the portal."
Freddy AI Agent uses Freshservice's Orchestration Center to connect to third-party systems, including identity providers, via workflow automation. An IT admin can configure a no-code flow that:
- Detects the password reset intent in a Slack message or service portal request
- Triggers an MFA verification step via the connected identity provider
- Issues the reset through the Orchestration Center's Active Directory or Azure AD connector
- Confirms the result to the user in the same channel
Freshservice reports 66% ticket deflection with Freddy AI Agent and a 77% decrease in average resolution time with Freddy AI Copilot assisting agents on the tickets that do require human handling.
Freshservice pricing:
| Plan | Price | Notes |
|---|---|---|
| Starter | $19/agent/month (annual) | Includes ServiceBot for Slack/Teams |
| Growth | $49/agent/month (annual) | Adds problem and change management |
| Pro | $99/agent/month (annual) | Adds sandbox, ITOM, advanced ITAM |
| Enterprise | Custom (contact sales) | Includes Freddy AI natively; 1,200 sessions/year included |
Freddy AI Agent is available as an add-on below Enterprise, but the complete automation experience (including the 1,200 AI sessions per year) is bundled into Enterprise. The 14-day free trial lets you test before committing.
For mid-market IT teams that want a modern, ITIL-aligned ITSM platform with AI automation included and faster time to value than ServiceNow, Freshservice is a strong fit.
Jira Service Management

Jira Service Management (JSM) includes a virtual service agent in its Premium and Enterprise plans, powered by Atlassian Intelligence. Password resets are explicitly listed as a use case in the virtual agent documentation: JSM's example intent walkthrough describes configuring a "Password reset" conversation flow where the bot asks which software the user needs to reset, then sends them the relevant instructions or triggers a web request to complete the reset.
The virtual service agent supports two configuration modes:
- Intent flows: pre-defined conversation trees for actions requiring guided steps or an automated web request (like actually executing a directory reset via API call)
- AI answers: generative AI answers from a connected Confluence knowledge base, good for self-service instructions the user can follow themselves
For a full automated reset (not just instructions), the intent flow with a web request step is the right approach. The web request step lets JSM call an external API, such as Microsoft Graph API for Azure AD or the Okta API, to complete the reset programmatically.
The Atlassian Community confirmed JSM's virtual agent on the portal supports automated actions via web request, specifically calling out "resetting a password, granting software access" as example use cases.
JSM pricing:
| Plan | Price | Notes |
|---|---|---|
| Free | $0 | 3 agents, no virtual agent |
| Standard | $20/agent/month | Includes Rovo AI; no virtual agent |
| Premium | $51.42/agent/month | Virtual service agent included (1,000 conversations/month) |
| Enterprise | Contact sales | 150 sites, unlimited automation |
For teams already in the Atlassian ecosystem (especially those using Jira Software and Confluence alongside their service desk), JSM Premium is a natural next step for automating password resets alongside incident and change management.
Where eesel fits for Slack-first IT teams

Most enterprise ITSM platforms are built around a ticketing portal first, with Slack/Teams bolted on. For IT teams that have made Slack the primary channel for support, where employees DM a bot instead of filing a ticket, the native integrations can feel like afterthoughts.
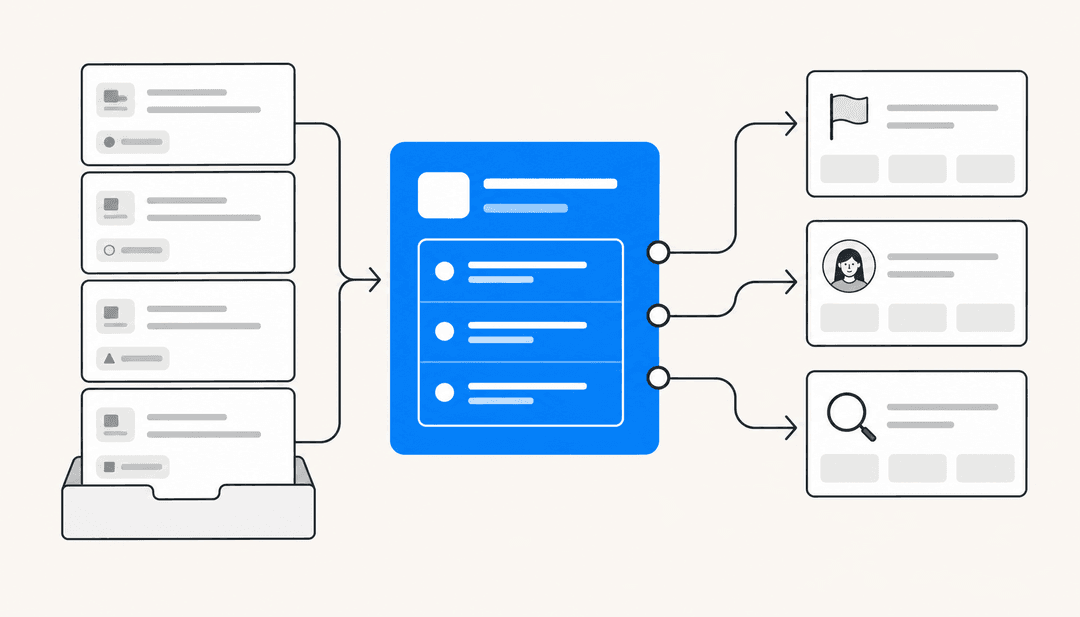
eesel AI takes a different approach: it's an AI agent layer that lives inside Slack and connects to your existing helpdesk rather than replacing it. For password reset automation specifically, eesel can:
- Detect reset requests from natural language in Slack DMs or channels
- Verify identity via MFA challenge (through a connected identity provider)
- Trigger the reset via integration with your directory service or existing ITSM platform
- Reply in the same Slack thread with confirmation
Because eesel charges $0.40 per task with no per-seat fees, smaller IT teams can get automated password resets without the cost structure of an enterprise ITSM license. The ticket deflection guide for Freshservice shows how eesel layers on top of an existing ITSM setup without displacing it.
For organizations running Zendesk or Freshdesk for helpdesk with Slack as the primary employee interface, eesel handles the Slack-side automation and routes anything that needs human involvement to the existing ticketing system.
Implementation guide
Getting from manual password resets to automated ones is a four-step process:
Map your current reset flow. Document the exact steps a technician follows today: how they verify identity, which system they use to issue the reset, how they notify the user. This becomes the spec for what you'll automate. Don't skip this step. It surfaces the edge cases (shared accounts, privileged users, foreign contractors) that need special handling.
Choose your verification method. For most organizations: MFA push challenge to a registered device for standard users, human approval for admins and privileged accounts. Make sure your chosen ITSM platform can trigger the verification method you use. If your MFA is in Okta, confirm the platform has an Okta connector that can issue a challenge, not just read user data.
Integrate with your identity provider. This is the technical step. You'll need to:
- Grant the ITSM platform API access to your directory (Active Directory, Azure AD, Okta, or Google Workspace)
- Configure the connector with the right permissions to read account status and write password resets
- Test with a staging account before going live
Most platforms (Freshservice Orchestration Center, JSM web request steps, Moveworks' native AD/Okta connectors) have documentation for this. The actual configuration is usually a few hours of work, not weeks.
Test, measure, then expand. Run the automated flow in parallel with manual handling for two weeks. Compare resolution time, error rate, and user satisfaction. Once you're confident in the base case (forgotten password, standard user, MFA verified), add complexity: account unlocks, temporary access grants, privileged account flows.
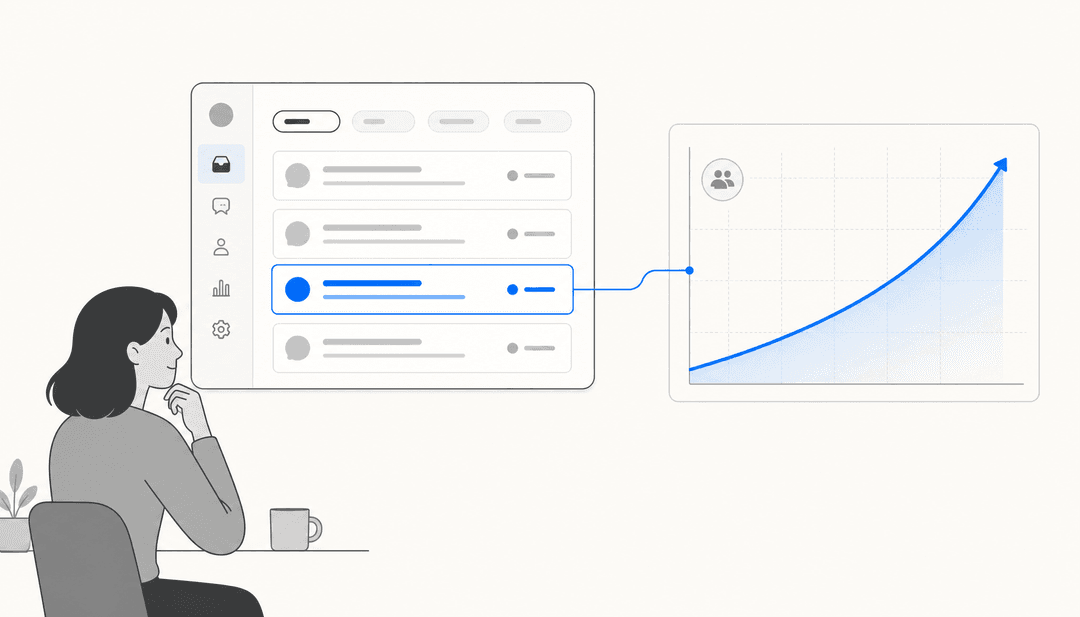
Metrics to track after going live
The question every IT manager gets asked after an automation rollout: "Is it actually working?" Here are the four numbers that matter:
Deflection rate. The percentage of password-related tickets resolved without any human involvement. A well-configured automated flow should get you to 60-80% deflection on password resets specifically. eesel's deflection rate guide covers how to calculate this and what benchmarks look like across ITSM categories.
Mean time to resolution (MTTR). Compare MTTR for password resets before and after automation. If the baseline is 45 minutes (including queue wait), a 2-minute automated resolution is a 95%+ improvement. This is the number that impresses leadership.
Cost per reset. With automation handling 70% of resets and reducing tech time on the remaining 30%, your average cost per reset drops significantly below the Forrester $70 benchmark. Calculate: (% auto-resolved × near-zero cost) + (% human-assisted × reduced-effort cost).
User satisfaction (CSAT). Automated resets get resolved faster, but sometimes users want confirmation a human looked at their issue. Track CSAT separately for automated vs. human-handled resets. A well-designed bot response (clear confirmation, immediate resolution) often scores comparably to human handling.
Password resets are one of the clearest wins available to IT teams investing in AI support ticket deflection. The volume is guaranteed, the process is consistent, and the automation technology is mature. The platforms that do it well (Freshservice, JSM, ServiceNow with Moveworks, and Slack-native tools like eesel) all handle the core flow reliably. The difference comes down to where your organization lives (Slack vs. portal), what identity provider you use, and whether you need the automation bundled into a full ITSM platform or layered on top of one you already have.
Start with the tickets that are already costing you the most and delivering the least satisfaction. Password resets are almost always at the top of that list.
Sources
- HDI Research Corner: Password-Reset Practices in Support
- Gartner estimate via BioConnect: 20-50% of help desk calls are password resets
- Forrester Research: $70 per password reset via Keeper Security
- Specops Software: Average organization saved $65K in 2023 with self-service password resets
- Freshworks: Freddy AI ITSM capabilities
- Freshservice pricing
- Atlassian: JSM virtual service agent guide
- Atlassian: JSM pricing
- ServiceNow ITSM Plans and Packages
- ServiceNow Autonomous Workforce announcement (February 2026)
- eesel AI pricing
- Atlassian Community: JSM virtual agent on portal supports automated actions
Frequently Asked Questions
Share this article

Article by
eesel writer team
The eesel writer team creates content to help support teams get the most out of AI.