How to fix Zendesk SSO issues: A complete troubleshooting guide
Stevia Putri
Last edited March 4, 2026
Single sign-on is supposed to make life easier. One set of credentials, seamless access, better security. But when Zendesk SSO stops working, it can lock your entire team out of your help desk. Suddenly, agents can't respond to tickets, admins can't manage settings, and customers're left waiting.
This guide walks you through diagnosing and fixing the most common Zendesk SSO issues. Whether you're dealing with Azure AD integration problems, certificate errors, or emergency lockouts, you'll find systematic solutions here.
Understanding Zendesk SSO and common failure points
Before diving into fixes, it's helpful to understand how Zendesk handles authentication. The platform supports three enterprise SSO methods:
- SAML The most common choice for corporate environments using Azure AD, Okta, or OneLogin
- OpenID Connect (OIDC) A modern alternative built on OAuth 2.0
- JWT Used for custom implementations where you control the authentication flow
Each method has specific configuration requirements, and most failures happen because of mismatches between Zendesk and your identity provider. The good news? These issues're usually fixable once you know where to look.
Emergency access: Regaining entry when SSO fails
Start with the worst-case scenario: your SSO service is down and nobody can log in. Before you panic, know that Zendesk provides emergency access methods.
Using the SSO bypass URL
If you've disabled Zendesk passwords and rely entirely on SSO, the account owner (and optionally all admins) can request a one-time access link.
Here's how it works:
- Navigate to
https://your_subdomain.zendesk.com/access/sso_bypass - Enter the email address associated with your Zendesk admin profile
- Check your email for a one-time access link (expires in 5 minutes)
- Click the link to gain immediate access without a password

One caveat: Some corporate spam filters automatically click links in emails to check for malicious content. If your filter does this, it may invalidate the access link before you can use it. In that case, contact your email administrator temporarily or try the alternative method below.
Accessing via normal authentication
If you haven't disabled Zendesk passwords entirely, you can still access your account through the standard login page:
- Go to
https://your_subdomain.zendesk.com/access/normal - Enter your Zendesk username and password
Keep in mind that your SSO credentials might differ from your Zendesk credentials. Your Zendesk username's always the primary email address listed in your user profile, which may not match your corporate login.
Configuring bypass access before you need it
The account owner can configure who has bypass privileges before problems occur. In Admin Center, go to Account → Security → Advanced, then click the Authentication tab. In the SSO bypass field, choose whether only the account owner or all admins can request emergency access.
This setting only appears when Zendesk authentication's turned off for team members, so configure it during your initial SSO setup.
Common Zendesk SSO error messages and solutions
Now let's tackle the specific errors that appear when SSO is misconfigured.
"AADSTS650056: Misconfigured application" (Azure AD/Entra)
This Azure AD error frustrates administrators more than almost any other. The error message suggests checking permissions for "AAD Graph," but the real culprit's usually a mismatch in your SAML configuration.
The actual cause: The Issuer value in your SAML request doesn't match the Identifier (Entity ID) configured in your Azure enterprise application. Even a small difference (like including or excluding https://)'ll break the authentication flow.
How to fix it:
- In the Azure portal, go to Enterprise Applications → Zendesk → Single sign-on
- Check the Identifier (Entity ID) field
- Compare it to what Zendesk is sending in the SAML request
- Update one or the other so they match exactly, including the protocol
The SAML request typically looks like this:
<samlp:AuthnRequest>
<Issuer xmlns="urn:oasis:names:tc:SAML:2.0:assertion">https://yourdomain.zendesk.com</Issuer>
</samlp:AuthnRequest>
Your Identifier in Azure must match that Issuer value character for character.
Certificate fingerprint issues: Another common Azure AD problem involves the certificate fingerprint calculation. Don't copy the thumbprint directly from Azure AD app settings. Instead:
- Download the certificate in
.cerformat from Azure AD - Calculate the SHA256 fingerprint using PowerShell:
Get-FileHash "Zendesk.cer" -Algorithm SHA256 - Enter that calculated value in Zendesk's Certificate fingerprint field
Source: Microsoft Entra ID troubleshooting documentation
"Please use one of the options below to sign in"
This error confuses many administrators because it appears even when SSO seems properly configured. The issue? You've enabled SSO for end-users but not for agents and admins.
Here's the fix:
- In Admin Center, go to Account → Security
- Select Team member authentication
- Enable External authentication and choose the SSO option
- Save your changes
This error often appears during testing when an admin tries to verify the SSO flow before rolling it out to the entire team.
Certificate and SAML metadata issues
Certificate problems cause a significant portion of SSO failures. Here are the most common scenarios:
Expired certificates: SAML certificates typically expire annually. When they do, authentication fails without warning. Set calendar reminders 30 days before expiration to rotate certificates proactively.
Fingerprint format errors: Zendesk requires the SHA256 fingerprint of your SAML certificate. Make sure you're using the correct hashing algorithm, some identity providers default to SHA1.
Entity ID confusion: The Entity ID (also called Identifier) must match exactly between your identity provider and Zendesk. Try these variations if you're stuck:
- With
https://prefix:https://yourdomain.zendesk.com - Without prefix:
yourdomain.zendesk.com
Some configurations work one way, others work the other way. The Microsoft community discovered this through trial and error when troubleshooting AADSTS650056 errors.
Step-by-step diagnosis workflow
When you encounter an SSO issue, follow this systematic approach to isolate the root cause.
Step 1: Verify IdP configuration
Start by confirming your identity provider settings match Zendesk's requirements exactly.
For Azure AD, verify:
- Sign on URL:
https://<subdomain>.zendesk.com - Identifier (Entity ID):
https://<subdomain>.zendesk.com - Reply URL:
https://<subdomain>.zendesk.com/access/saml
For Google Workspace:
- Install the Zendesk SSO app from the Google Workspace Marketplace
- Configure SSO within the Zendesk app, not Google's security interface
- Set the Entity ID with the
https://prefix initially, then try without if issues persist
Step 2: Validate SAML assertions
Browser developer tools are your friend here. Open Chrome DevTools or Firefox Developer Tools before attempting to sign in. Watch the Network tab for SAML requests and responses.
Look for:
- The Issuer value in the SAML request
- Any error messages in the SAML response
- HTTP status codes (302 redirects, 400 errors, etc.)
This information often reveals exactly where the authentication flow breaks.
Step 3: Test authentication flow
Don't just test with one user type. Verify SSO works for:
- End users (customers submitting tickets)
- Agents (staff responding to tickets)
- Admins (managing settings)
Also test across different access methods:
- Direct Zendesk URL
- Mobile app (iOS and Android)
- Host-mapped domains (if you use custom domains)
Step 4: Review Zendesk security settings
In Admin Center, confirm:
- External authentication is enabled for the appropriate user groups
- The correct SSO configuration is selected as primary
- User permissions and roles are properly assigned
Remember that users authenticating through end-user SSO're assigned the role specified in your Zendesk settings, which may include team member access if not configured carefully.
Prevention: Best practices for stable SSO
Fixing SSO issues is important, but preventing them saves even more time.
Configuration management
- Document everything: Keep a record of your Entity ID, certificate fingerprints, and all URL configurations. When something breaks, you'll have a reference point.
- Test before go-live: Always test SSO in a non-production environment first. Zendesk provides testing features for this purpose.
- Maintain backup access: Ensure at least one admin account has bypass capability configured.
- Monitor certificate expiration: Set calendar reminders 30 and 7 days before certificate expiry.
User management
Email verification's critical when using SSO. The email addresses from your identity provider must match exactly what's configured in Zendesk. Mismatched emails're a common source of "user not found" errors.
If you're using automatic user provisioning via SCIM, verify that user attributes map correctly between systems.
Security considerations
When you enable enterprise SSO, you're responsible for verifying user identities. Zendesk stores only the name and email address by default, though you can sync additional data like organization membership.
If you turn off Zendesk authentication entirely, all Zendesk passwords're permanently deleted within 24 hours. Make sure your SSO's rock-solid before taking this step.
When to consider alternatives to native Zendesk SSO
Native SSO works well for many organizations, but it has limitations. Complex multi-brand setups, advanced user provisioning requirements, or compliance needs sometimes call for different approaches.
Third-party identity management tools can provide additional features like:
- More granular access controls
- Better audit logging
- Support for complex organizational structures
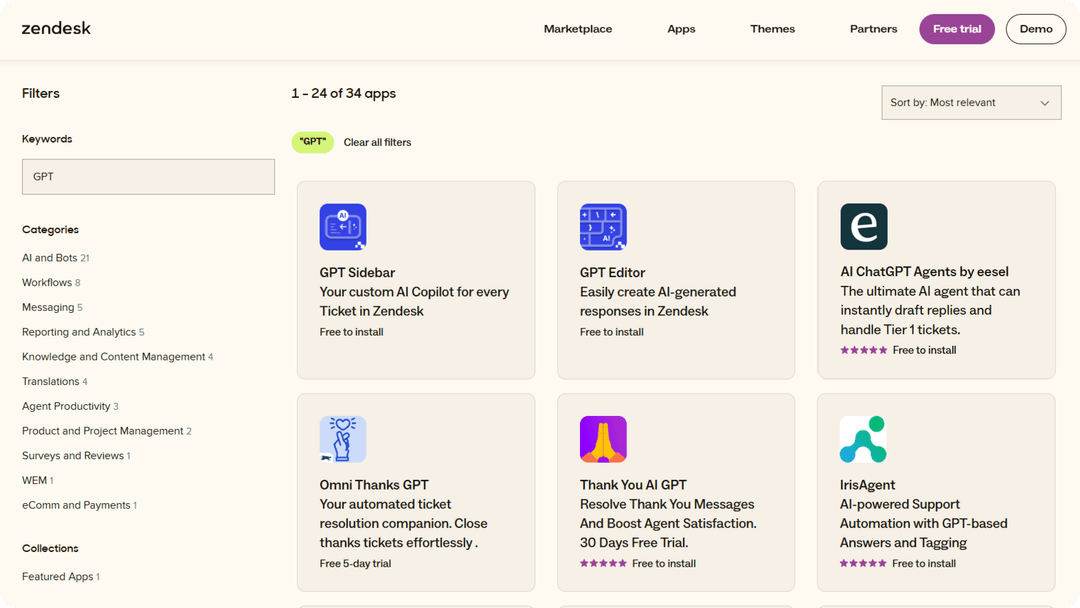
At eesel AI, we take a different approach to authentication. Instead of complex SAML configurations and certificate management, our AI teammate for customer service integrates directly with your existing help desk. You don't need to configure SSO because eesel works within your current Zendesk environment, learning from your past tickets and help center articles without additional authentication layers.

Our customers often tell us they switched to eesel because they were tired of managing SSO configurations that kept breaking. With eesel, your agents continue using Zendesk exactly as they always have. The AI simply helps them draft better responses faster, no additional login flows required.
If you're spending more time troubleshooting SSO than actually helping customers, it might be worth exploring whether your current setup's the right fit for your team's needs. You can try eesel AI free or book a demo to see how our AI Copilot helps agents draft better responses faster.
Resolve your Zendesk SSO issues today
SSO problems are frustrating, but they're rarely permanent. Start with the emergency access methods if you're locked out, then work through the error-specific solutions based on what you're seeing. Most issues boil down to configuration mismatches that can be fixed with careful attention to detail.
Keep this guide bookmarked for the next time something goes wrong. And remember: document your working configuration once you get it stable. Future you'll thank present you when the next certificate renewal comes around.
If you've tried everything here and still can't get SSO working, it may be time to contact Zendesk support with your specific error messages and HAR files captured from browser developer tools.
Frequently Asked Questions
Share this article

Article by
Stevia Putri
Stevia Putri is a marketing generalist at eesel AI, where she helps turn powerful AI tools into stories that resonate. She’s driven by curiosity, clarity, and the human side of technology.